Preface
In response to the digital era, the Financial Supervisory Commission (hereinafter referred to as the FSC) promulgated the Financial Cyber Security Action Plan in August 2020 and implemented related measures. However, given the importance of financial cybersecurity resilience, which has been enhanced during the period of the Action Plan’s implementation through the digital transformation driven by the COVID-19, the intensification of the cybersecurity threat, major disasters, and geopolitical risks, the FSC has reviewed the Action Plan on a rolling basis, and has expanded and refined the various implementation measures to continue to promote the digital transformation of financial institutions, the development and utilization of financial technology, as well as the innovation and opening up of financial services, while ensuring to provide financial services that are safe, convenient, stable and uninterrupted to the public. The Financial Cyber Security Action Plan proposes various implementation measures to achieve the goals of the Action Plan in four major aspects: strengthening cybersecurity supervision, deepening cybersecurity governance, enhancing cybersecurity resilience, and utilizing cybersecurity joint defense: Among them, building an organizational culture that emphasizes cybersecurity, enhancing the capacity and standard of cybersecurity governance, and ensuring the continuous functioning of the system and the data safety is one of the important aspects of the Financial Cyber Security Action Plan. To support the promotion of the Financial Cyber Security Action Plan, the Company has been assisting securities firms in assessing their cybersecurity governance maturity level since 2022 to achieve the goal of deepening cybersecurity governance. In order to continue to refine the content of the cybersecurity governance maturity assessment described in the previous paragraph, in 2023, we expanded the targets of the maturity assessment so that we could understand the cybersecurity governance maturity practices implemented by major securities firms in the securities market and could analyze and assess the results of the assessment in order to make rolling adjustments to the cybersecurity counseling measures so as to enhance the capability of cybersecurity protection.
Implementation Status of the Company
The securities industry has adopted the Cybersecurity Assessment Tool (hereinafter referred to as CAT) released by the U.S. Federal Financial Institutions Examination Council (FFIEC) as the cybersecurity assessment tool for the financial industry to assess the maturity of its security governance. In 2020, F-ISAC’s Financial Cybersecurity Maturity Assessment Program under the Financial Cybersecurity Action Plan also adopted the aforementioned assessment tool to assess the cybersecurity maturity of financial institutions in Taiwan. Considering the consistency, the FFIEC CAT tool is used to identify the inherent risk level and network security maturity, the relevant evaluation process and description are as follows:
1. Identify the Inherent Risk
In this case, we adopted FFIEC CAT’s Inherent Risk Questionnaire for securities firms to fill out in order to identify their inherent risks, which can be divided into five categories. We examined several aspects including external services provided by the organization and internet connection, in order to understand the situation of the inherent risks borne by securities firms, which are described as follows:
(1) Internet Technology and Connection
The specific technologies and products used by an organization would affect the inherent risk level. This assessment includes the number of ISP connections, the number of non-secure external connections (e.g. FTP), wireless access, the number of personal devices allowed to connect to the corporate network, etc. These external connections have potential risks to the organization and are included in the assessment.
(2) External Service Channels
The diversity and number of financial services channels an organization offers would affect the inherent risk level. This assessment includes online account opening, electronic ordering services, as well as online customer service, billing inquiries, and so on.
(3) Online and Mobile Financial Products and Services
The technology used and the percentage of online account opening and electronic ordering services provided by an organization may also result in different levels of inherent risk; whether or not the organization provides IT hosting services for other organizations may also affect its inherent risk.
(4) Organizational Characteristics
Organizational structure and environment would affect the inherent risk level. The categories of assessment include mergers and acquisitions, number of employees, number of network security providers, security personnel, number of personnel with privileged access, changes in the IT environment, changes in the geography of business operations, and location of operations/data centers, etc. Privileged access to the system is also examined in this category.
(5) External Threats
The number, type, and complexity of attempted or successful attacks targeting an organization will affect the inherent risk exposure. This assessment includes the frequency with which an organization receives phishing attacks and the number of cyberattacks it suffers, etc. The inherent risk of this category is greater for some specific institutions or organizations than for others.
By reviewing the above categories, the inherent risks of securities firms can be identified, which in turn corresponds to their respective risk levels.
2. Calculate the Overall Inherent Risk Level
Based on the calculation of the above five aspects, the organization can be classified into five Inherent Risk Levels (IRLs), which indicate the inherent risks that the organization is exposed to and should have corresponding cybersecurity controls, as described below:
(1) Least: The use of IT in the organization is extremely limited, with a very few computers, applications, and systems in use, and no connections between computers or systems. Products and services are simple; the organization has a limited service geography and a limited number of employees, so the risk is low.
(2) Minimal: The organization is somewhat limited in the complexity of the technology it uses and provides somewhat low-risk products and services. The organization’s key business systems are outsourced and primarily use technology that has been built and developed, with limited complexity, to maintain few connections with customers or third parties, and therefore, the risk is minimal.
(3) Moderate: In terms of quantity and complexity, this type of risk involves the use of slightly more complicated technologies by the organization. Organizations may outsource key business systems and applications, or provide a greater number and diversity of products and services through multiple channels, so the risk is moderate.
(4) Significant: Using complex technologies, an organization may use emerging technologies to deliver high-risk products and services, and may offer a significant number of applications internally. Organizations that allow using significant volumes of personal devices, or a wide range of device types, and maintain significant connections with customers and third parties, or provide a wide range of payment services by themselves rather than through a third party, and may have significant transaction volumes, are at greater risk.
(5) Most: An organization uses extremely complex technology to deliver various products and services; most of these products and services carry a high level of risk. Organizations may outsource certain critical business systems or applications, but the majority of these are handled internally, or the organization maintains multiple connection types for data transfer with customers and third parties; therefore, the risk is the greatest.
3. Confirm the Target Maturity Reasonable Zone
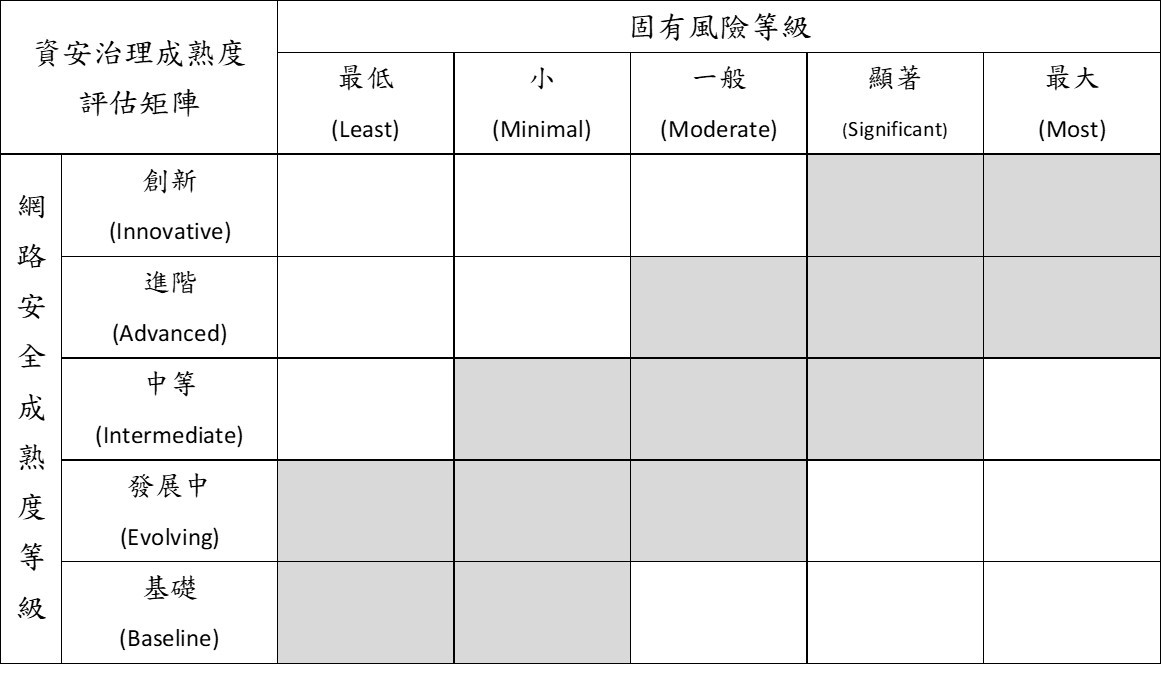
As shown in the figure below, based on the inherent risk and maturity relationship matrix provided in the FFIEC CAT, the greater the overall inherent risk level of the organization, the more mature its cybersecurity maturity level should be. If the overall inherent risk level is the lowest (Least), the reasonable zone for the organization to develop the cybersecurity maturity target should be set at “Baseline” to “Evolving” level. If the overall inherent risk level is small (Minimal), the reasonable zone for the organization to develop a cybersecurity maturity target should be set at the “Baseline” to “Intermediate” level. Therefore, after identifying the overall inherent risk, it is possible to correspond to a reasonable zone of maturity level for the organization’s target by referring to the matrix of inherent risk and maturity relationships provided in the FFIEC CAT.
4. Determining Network Security Maturity Levels
FFIEC CAT divides the Cybersecurity Maturity Questionnaire into five major assessment categories: cyber risk management and supervision, threat information management and sharing, cybersecurity management, outsourcing and dependency management, and cyber incident management and response. The questions in each category are then classified into five levels in order to calculate the network maturity level, which is described as follows:
(1) Baseline: The organization meets the minimum expectations as required by law and regulation, or as recommended by supervisory guidance. This level includes legal compliance objectives. Management has reviewed and evaluated the guidelines and principles.
(2) Evolving: Additional documented procedures and policies are in place that are not explicitly required. The organization has considered implementing a risk management orientation, cybersecurity responsibilities have been formally assigned, and the scope of protection extends to customer information, including the integration of information assets and systems.
(3) Intermediate: Detailed and documented procedures have been formulated and highly implemented; in addition, risk management practices and analysis have been integrated into the business operation strategy.
(4) Advanced: Network security practices and analyses are integrated in a cross-unit or cross-business approach, most risk management processes have been automated and include continuous process improvement; the responsibility for risk decision-making in front-line business has been formally assigned.
(5) Innovative: Managing cyber risk by promoting innovation in people, processes, and technology for organizations and industries. This may mean developing new controls, new tools, or creating new platforms for information sharing, and real-time, predictive analytics are all relevant to automated responses.
5. Network Security Maturity Variance Analysis
The achievement rates of the five major assessment categories, including cyber incident management and response, correspond to the organization’s maturity level in each category. Finally, we analyze the difference between the calculated maturity level of each assessment category and the assessment questions within a reasonable zone of the organization’s target maturity level to confirm the conformity between inherent risks and cybersecurity maturity level and analyze the discrepancy. In this case, there are still discrepancies between the network maturity level of the securities firms and the risks they are exposed to, and we understand that the former securities firms still need to strengthen some of these aspects. We also provide references for securities firms to strengthen their cybersecurity measures in accordance with current regulatory requirements, industry development, and organizational resources, so that we can review the improvement situation of these firms again in the future.
Results Promoted by TWSE
1. Considering the practice and current status to analyze thoroughly
In addition to analyzing the results of the network maturity assessment and recommending that securities firms continue to strengthen the relevant fields and aspects, we also take into account recent trends in cybersecurity and practical work, and review the questions in the maturity questionnaire in seven dimensions: automation tools, identities, outsourcing/suppliers, vulnerability scanning, intelligence, configuration management, and equipment/endpoint management. The securities firms showed a high rate of achievement in the questions on outsourcing/suppliers, intelligence, and equipment/endpoint management, indicating that the firms have already achieved a high level of protection in these aspects.
2. Improving Cybersecurity-Related Standards
The Company comprehensively reviewed the content of the security governance maturity questionnaire. Based on the practical operation and reference to other regulatory requirements, the Company selected the questions as reference for the revision of security-related regulations for securities firms, in order to improve the security management and control operation and strengthen the cybersecurity protection capability in the securities market.
Epilogue
TWSE has been continuously promoting securities firms to strengthen their cybersecurity by cooperating with the competent authority over the past few years. Not only does TWSE counsel securities firms to implement IPS/WAF cybersecurity equipment to enhance their protection capability, but also adopts various management methods, such as the network maturity assessment in this case, to measure the maturity of the security governance for securities firms, and to understand the strengths and weaknesses of important securities firms, which can then be used as the basis for subsequent counseling and the improvement of the cybersecurity regulations. Overall, to strengthen the security of securities firms requires a comprehensive review in order to know the enemy and know ourselves well so that we will never be defeated. The Company has also implemented and continued to strengthen various measures under the Financial Cyber Security Action Plan in response to the current situation, and has adjusted its counseling measures on a rolling basis, in order to build a sound capital market in conjunction with the competent authority and the securities industry, thereby providing the public with peace of mind, convenience, and stable and uninterrupted financial services.
