Preface
According to market statistics from the Taiwan Stock Exchange (hereinafter referred to as the TWSE), as of the end of December 2023, electronic securities orders accounted for over 78% of market transactions, indicating that the popularity of the internet has gradually transformed market structure and investor behavior. However, internet threats have also grown rapidly at the same time. From early computer viruses to advanced persistent threats (APTs) today, the forms of Internet attacks continue to evolve and have become more complex. In order to protect individual, corporate, and national security, there is a strong demand for information security professionals with professional skills and risk management capabilities from government agencies and enterprises around the world, as well as an increasing emphasis on international information security certifications. Nowadays, information security talents have become an indispensable asset within organizations. The promotion and development of professional talents help enterprises construct more comprehensive information security defense strategies, and further assist enterprises in passing international information security verification to enhance their reputation and market competitiveness.
Exploring the Core Knowledge and Professional Scope of Key Information Security Certificates Among Various Types of Information Security Certificates
To strengthen the cultivation of information security talents, The Financial Supervisory Commission (hereinafter referred to as the FSC) released three measures in the “Financial Cyber Security Action Plan 1.0” in August 2020, and the first measure is to establish a functional map for information security talents. The FSC later released the “Functional Map of Information Security Talents” in June 2021 to divide talents into three major sections (supervision and governance, security development, and information security operations), which is also a common way for information security units to group their functions.
Today, there are quite a variety of information security professional certificates promoted by various information security professional associations, and even large information and information security enterprises will release relevant certificates for their own products, such as Cisco’s network equipment or Amazon’s cloud computing services (AWS), allowing customers to use related products more securely as solutions for enterprises.
Different information security certifications correspond to specific job functions and areas of expertise, which can be roughly divided into “information security governance” and “information security technology operations.” Sub-fields include risk management strategies and IT auditing for governance, forensic investigation and security development processes for technology. These certifications provide individuals with specialized skills across various dimensions of their professional careers.
The importance of information security certification is no less than practical work experience. Through the certification preparation process, in addition to filling the gap in information security knowledge, most institutions require the holder to continue professional training after passing the test, including professional development activities such as special-topic seminars and cyber security conferences to accumulate sufficient training hours, in order to timely update and continuously improve on emerging information security knowledge and skills.
At present, the application and maintenance requirements for different information security certificates vary, and the specifications of relevant certificates need to be referred to for specific details. Generally, it is common for applicants to have a combination of relevant background, education, and accumulated work experience in related fields to ensure that they have the ability to combine theory with practical operations. Furthermore, due to the multitude of information security certificates, it is recommended to refer to the latest “List of Cyber Security Professional Certificates” released by the Administration for Cyber Security, moda to determine the priorities of preparation.
Taiwan Has Released the List of Professional Information Security Certificates, Aiming to Build Solid Information Security Talents and Skills
The government has established the Administration for Cyber Security, moda (hereinafter referred to as the ACS) as a dedicated unit, which has listed the country’s information security as an important and critical field. The updated “List of Cyber Security Professional Certificates” announced by the ACS is helpful for government agencies and enterprises to refer to. The implementation of a standardized certification system to enhance the professional level of information security professionals can not only cultivate internationally competitive cyber security professionals, but also encourage various units to pay more attention to the certification and training of employees’ information security capabilities.
The list above divides certificates into the two categories of management and technology, and lists internationally trusted issuing agencies (such as ISC², CompTIA, ISACA, Offensive Security, Cisco, etc.) and relevant certificates issued by the Ministry of Economic Affairs. Enterprises may refer to this list for different scenarios, for example:
- Design external talent requirements and internal personnel promotion standards to ensure that they possess the professional knowledge and skills required for the position.
- Establish an internal talent on-the-job training plan and reward system for selection of professionals who possess the improved professional skills for certification based on the development path of the information security function, in order to be conducive to cultivating professional talents who meet certification requirements.
- Optimize third-party management. When selecting information security solutions or services, the information security capabilities of external partners or suppliers can be evaluated based on the certificate list to ensure service quality and reduce potential risks.
The “List of Cyber Security Professional Certificates” includes relevant certificates from the beginner to the advanced level. The following is a highlight of the information security certificates that the market closely pays close attention to:
CISSP (Certified Information Systems Security Professional)
- CISSP covers eight core fields of information security and is a certification that combines breadth and depth in the information security field. It discusses the formulation of information security strategies and risk management to ensure the stability of the enterprise’s information security framework, and focuses on designing and implementing a security framework to prevent attacks, covering communication and network security protection, rigorous identity verification and authorization mechanisms to ensure reasonable access permissions and prevent network attacks. Emphasis is also placed on the incorporation of security considerations into each stage of the software development lifecycle, performance of information security checks and risk assessments, verification of the effectiveness of security measures, and continuous information security monitoring and development of incident response strategies to ensure timely response to information security threats.
- Suitable roles:A combination of the governance and technology types, suitable for chief information security officers and the information security management level.
- Issuing agency:ISC² (International Information System Security Certification Consortium).
CISA (Certified Information Systems Auditor)
- CISA focuses on the process of information system auditing, including audit strategies, risk assessment techniques, and design and execution of audit plans, and emphasizes the evaluation of control effectiveness to ensure that risk-based methods can be applied in audit operations to protect the confidentiality, integrity, and availability of information systems. In addition, this certification also includes an understanding of information technology, covering system development and maintenance, management of information system infrastructure, as well as implementation of effective audit and control measures in the technical environment.
- Suitable roles:The governance type, suitable for information security risk management personnel and IT auditors.
- Issuing agency:ISACA (Information Systems Audit and Control Association).
OSCP (Offensive Security Certified Professional)
- OSCP focuses on the application capabilities on network attacks and penetration testing, emphasizing the mastery of how to identify and exploit vulnerabilities from the initial investigation stage by sniffing weak points in system defense to in-depth penetration attacks; it completes penetration tasks in a controlled environment, and provides detailed reports to demonstrate its application capabilities in real-life scenarios.
- Suitable roles:The technical type, suitable for information security penetration and vulnerability evaluation engineers, and red team personnel in an information security attack.
- Issuing agency:Offensive Security.
On the other hand, in addition to the certificates on the list, there are some certificates that include individual and organizational level international certification for information security management systems and continuous operations management systems. These help organizations to introduce management system frameworks, combine the continuous improvement management mechanism (PDCA), establish organizational goals, and improve in a circular process based on the results of implementation reviews to achieve effective risk control management goals. The relevant important certifications are listed as follows:
ISO/IEC 27001 (Information Security Management Systems)
- ISO/IEC 27001 emphasizes maintaining an information security management system suitable for enterprises. It aims to develop clear information security policies, assess the expectations of internal and external stakeholders, establish quantifiable information security goals, and determine acceptable risk levels for the enterprise to deploy security control measures and documented standard procedures from various aspects such as physical security, personnel security, data security and incident reporting, and ensure the effective operations and continuous improvement of the information security management system through regular internal audits and monitoring.
- Suitable roles:The governance type, suitable for information security practitioners and IT auditors.
- Issuing agency:ISO (International Organization for Standardization).
ISO 22301 (Business Continuity Management Systems)
- ISO 22301 focuses on the establishment and maintenance of the business continuity management system (BCMS) to ensure uninterrupted business operations in various unexpected events by formulating a global business continuity strategy. Through risk assessment and operational impact analysis, it helps organizations identify and evaluate various risks and their potential impact on business, and develops corresponding response plans. The business recovery plan and exercises include emergency team preparation and actual testing of the feasibility of the business recovery plan, in order to ensure that operations can be quickly resumed within a tolerable time after a major incident occurs.
- Suitable roles:The governance type, suitable for information security and continuous operations practitioners, and IT auditors.
- Issuing agency:ISO (International Organization for Standardization).
TWSE Spares No Effort in Promoting Information Security Certification
In compliance with the “Financial Cyber Security Action Plan 2.0” of the FSC, the TWSE encourages securities firms to expand the introduction of international information security management standards and deploy information security talents with diverse expertise. At present, the securities industry’s requirements for information security certification are standardized in the “Standard Specification for the Internal Control System of Securities Firms,” the “Establishment of Securities Firms’ Cyber Security Inspection Mechanism” and their appendices, and are divided into two aspects: one is that securities firms should obtain cyber security management system certificates, and the other is that securities firms’ information security personnel should hold a certain number of cyber security professional certificates, and be managed using the securities firm rating system.
According to the “Standard Specification for the Internal Control System of Securities Firms,” the current regulations related to information security certificates are as follows:
- CC-12000 Information Security Policy (8):The company shall import the information security management system into its core system according to its information security rating, and pass the verification by a fair third party and continuously maintain the effectiveness of the verification.
- CC-13000 Security Organization (7):The company shall require its information security personnel to obtain and maintain equivalent information security professional certificates in accordance with their respective information security classification requirements.
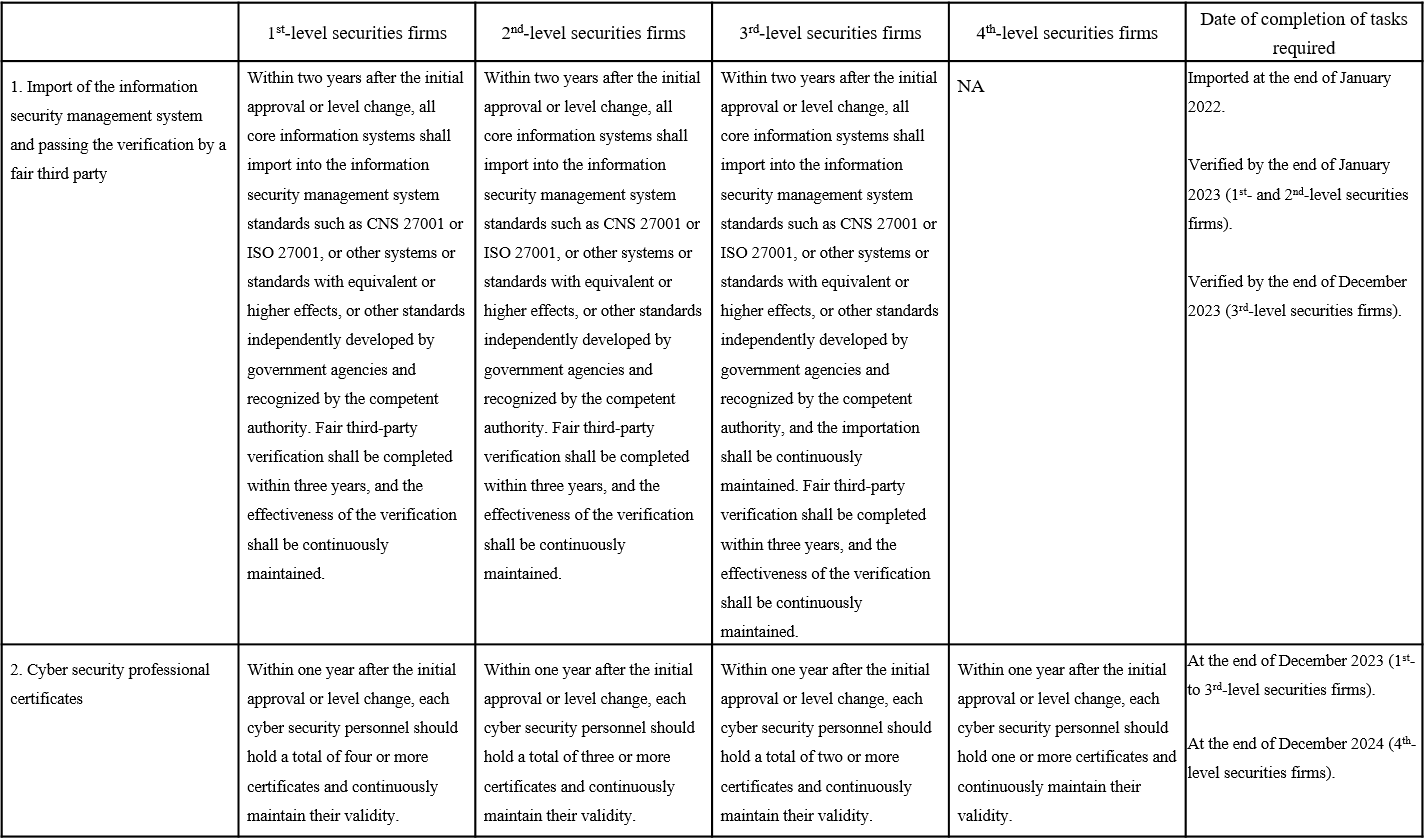
- In addition, according to the “Establishment of Securities Firms’ Cyber Security Inspection Mechanism” and its appendices, the current regulations related to information security certificates are detailed in the following table:
In order to assist securities firms’ information security personnel in obtaining certificates, the TWSE has also launched a number of professional certification courses for securities firms’ cyber security personnel this year (2024), and invited external professional training institutions to provide commentary on the ISO 27001:2022 information security management system, and any fourth-level securities firm with its information security personnel successfully obtaining the certificate after the course may apply for an incentive payment from the TWSE. As of now, more than 20 securities firms’ information security personnel have obtained the professional certificate to effectively enhance their professional abilities and strengthen the overall information security level of securities firms. In addition, in response to the transformation measures of intelligent supervision, the TWSE has established an electronic filing platform and held a briefing on July 3 to request securities firms’ regular filing every six months, including the number of international information security verification certificates obtained by each securities firm and the number of professional information security certificates obtained by information security personnel, in order to comprehensively grasp the status of implementation by each securities firm and implement the necessary measures for handling information security classification and protection.
Conclusion
The FSC and the ACS have respectively released the “Functional Map of Information Security Talents” and the “List of Cyber Security Professional Certificates” to provide clear guidance for the training and certification of professional talents in the field of information security. This not only provides a clear career development path for information security personnel, but also greatly promotes the popularization and standardization of information security certification in Taiwan. The TWSE is also committed to assisting industry participants with the goal of enhancing the overall information security professional level of the securities industry and its ability to respond to cyber threats.
From information security governance to information security attack and defense technology, diverse information security certifications provide systematic and comprehensive learning and development opportunities for enterprises and employees. Obtaining relevant international information security certifications is not only a validation of existing knowledge, but the gradual honing of skills and accumulation of new knowledge in the process is also a crucial step in aligning with international information security standards. The enhancement of information security talents’ expertise not only contributes to their personal career growth, but also creates a more stable and secure trading environment for enterprises and the overall market, which should have positive effects on the sustainable development of enterprises and the protection of market security.
